Managed network service providers (MNSPs) and their particular issues don’t generally keep me awake at night. But in a world of SD WAN disruption and its tendency towards less and less visibility for MNSPs due to more and more closed boxes littering the last mile landscape, those MNSP engineers aren’t getting a whole lot of sleep when it comes to dealing with last mile delivery issues.
Network insight has been all the rage over the last couple of years, but that telemetry is generally exclusive to the equipment owners – leaving MNSPs, who have no access to the hardware, in the dark. As this problem becomes increasing prevalent, many of the tools designed to shine light on this issue require expensive tooling and complex integrations.
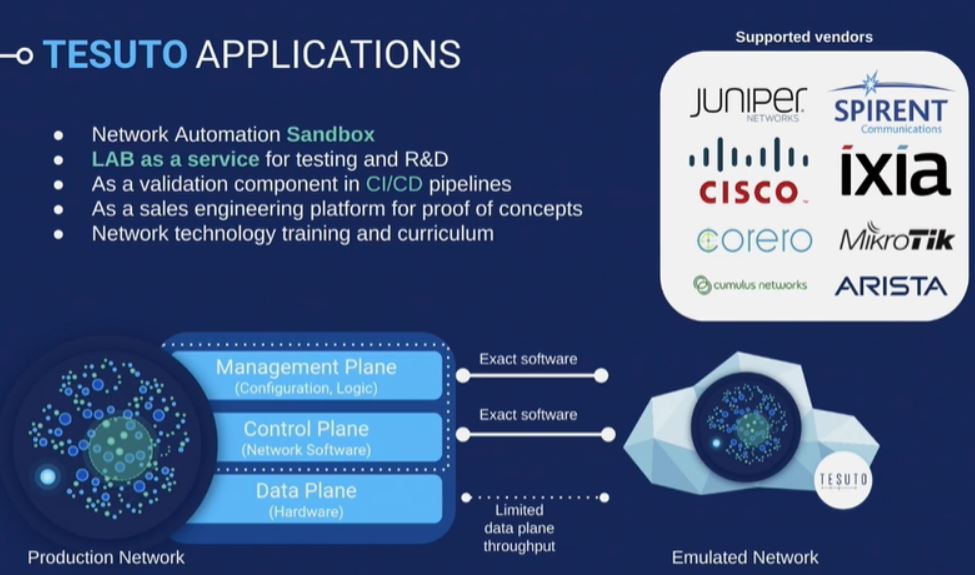
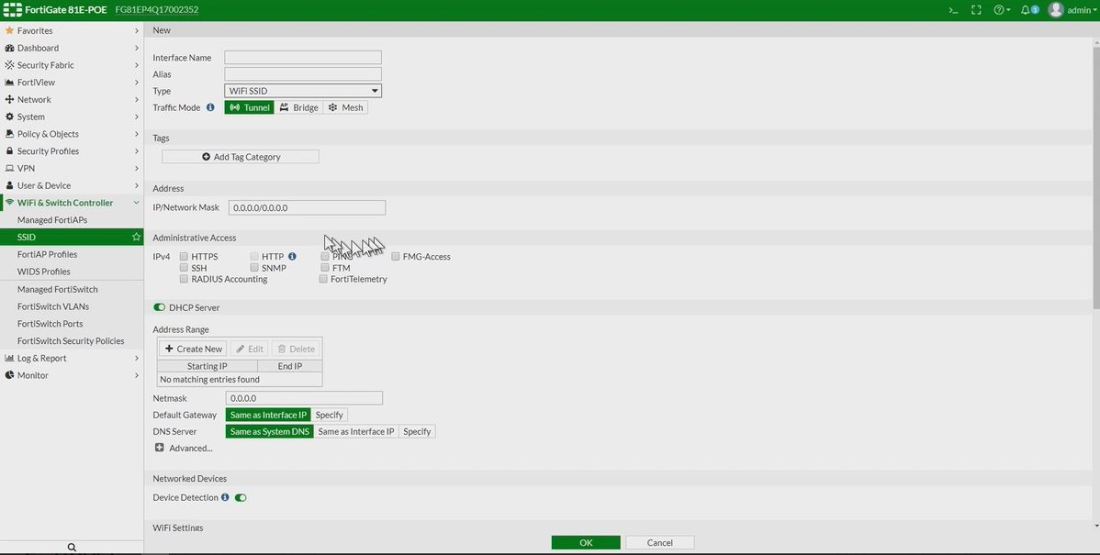
Ixia’s newly announced IxProbe offers itself as an operationally simplistic approach to this visibility gap. In a small form factor that takes minutes to install inline, IxProbe provides traffic stats, link status, and when used in conjunction with Ixia’s Hawkeye, a battery of QoS and link quality tests.
Below are just a few features this test probe brings to the table.
-
- Can be installed by non technical resources in the field
- Both active and synthetic test capable
- Adopts the IP address of the router (watch this video at the 7 min mark for a good discussion on how this works)
- Fail-to-wire (if the device fails, your link doesn’t)
- Only answers to your configured whitelist of management IP
- APIs for network management system integration
IxProbe isn’t just for MNSPs, and it’s not just for inline testing. While you probably have a myriad of other monitoring solutions, networking probes, and QoS testing devices inside your own network, it’s worth noting that the IxProbe performs tests out of band and can easily be deployed throughout branch networks and other edge locations, perhaps as an option for unifying your test probe solution.
There is a 1 gig limitation on the device, though, so beware you won’t be using this to analyze performance on those big ole backbone links.
If you’re interested in more information on the IxProbe and how it fits into the rest of the Ixia testing and monitoring portfolio, be sure to check out both of these short TFD21 videos here.
You can also find the data sheet here: https://www.ixiacom.com/resources/ixprobe-active-sla-monitoring-service-providers-and-enterprises
Disclaimer: While Networking Field Day, which is sponsored by the companies that present, was very generous to invite me to the fantastic NFD21 event and I am very grateful for it, my opinions are totally my own, as all redheads are far too stubborn to have it any other way.
Published 10/26/2019